Amazing Collection of online role playing games for your website!
Pimp Attack
Rating
Technical Details
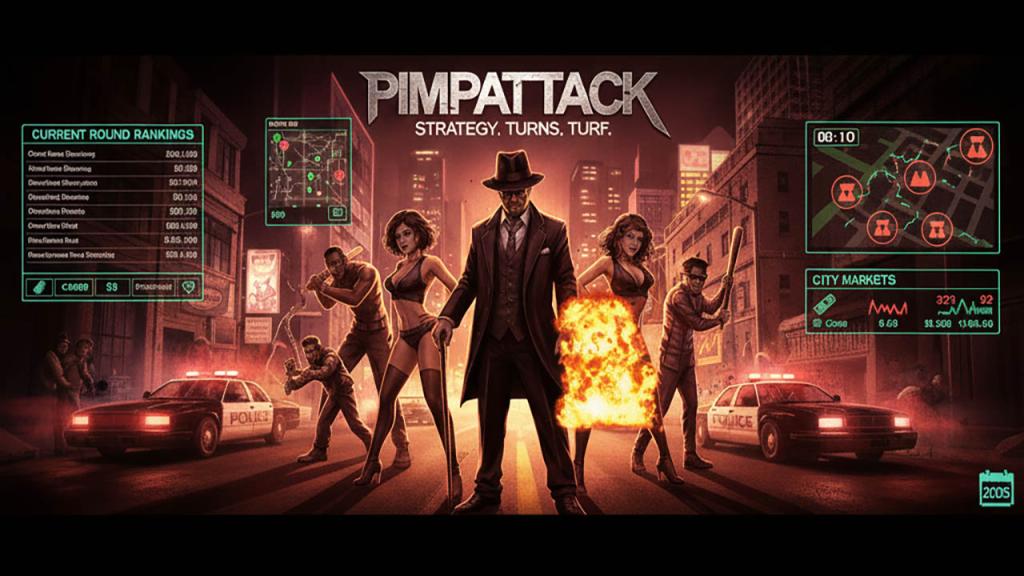
Battle for prestige and profit in a fast-paced, turn-based urban strategy game. Build your crew, outsmart rival factions, and climb the rankings across concurrent rounds with evolving cities, markets, and leaderboards.
This is a mature-themed 2000s-era competitive experience focused on resource management, crew tactics, and turf control. Expect tight timers, round resets, and a meta driven by alliances, city choice, and smart use of turns.
File Verification
PimpAttack - Browser-Based Pimp/Gangster Game - Game Analysis Report
1. IDENTITY & METADATA
Name: PimpAttack
Version: Unknown (no version file found)
Genre: Pimp/Gangster MMO (Urban crime theme)
Type: Web-based multiplayer strategy game
Developer: Unknown (anonymous)
Website: pimpattack.com (copyright © 2004)
Alternative Version: "tru" subdirectory by Core Games (coregames.co.uk)
Database Date: February 28, 2005 (SQL dump timestamp)
License: Not specified
THEME: Urban crime simulator where players manage prostitutes ("hoes"), thugs, weapons, and drugs to build criminal empires. Similar to Pimpwar and Kings of Chaos. Features crew (gang) system, city-based gameplay, and competitive rankings across multiple game rounds.
ETHICAL NOTE: This represents 2004-era "shock value" browser gaming. Controversial subject matter (prostitution, violence, drugs) typical of mid-2000s edgy online games.
2. CODEBASE STATISTICS
File Composition
- 80 PHP files (6,954 total lines) - medium codebase
- 8 GIF files (64 KB) - game graphics
- 6 JPG files (266 KB) - images/photos
- 2 CSS files (1.45 KB) - minimal styling
- 2 BMP files (6 KB)
- 2 SQL files (67 KB) - database schemas
- 2 INC files (1.67 KB) - includes
- 483 timestamped image files (unusual naming: .gif1096810374, .jpg1098455668, etc.) - uploaded user content?
- 1 PSD file (142 KB) - Photoshop source (pimpattacklogo.psd)
- 1 .htaccess file (0.37 KB)
- Total: 589 files
Largest PHP Files
- crew.php (428 lines) - crew/gang management system
- awards.php (374 lines) - achievement/awards system
- admin.php (306 lines) - admin control panel
- funcs.php (271 lines) - core functions
- purchase.php (269 lines) - store/buying system
- credits.php (234 lines) - premium credits (PayPal integration)
- html.php (205 lines) - HTML templates and headers
- pimp.php (186 lines) - player profile display
- install.php (181 lines) - installation system
- signup.php (180 lines) - registration with 4-step process
Database Schema (1,556 lines SQL)
Core tables:
- users - Main account table
- games - Round configuration (type, speed, starts/ends times)
- bans - Banned IP/users with reasons
- censors - Censored words
- html - Rules, ToS, guide, descriptions
- news - News posts
- paypal - Payment transactions
- stat - User statistics per round
Per-Round tables (r10_, r11_, etc.):
- r#_board - Message board (crew, public, attack boards)
- r#_city - Cities (id, name, country)
- r#_contacts - Friends/enemies lists
- r#_crew - Gangs/crews (name, founder, members, icon, networth, rank)
- r#_cronjobs - Automated tasks (lastran timestamps)
- r#_invites - Crew invitations
- r#_mailbox - Private messages
- r#_pimp - Player data (extensive 70+ columns!)
- r#_statlog - Statistics tracking
- r#_user_crews - User-crew relationships
- r#_wanted - Attack/hit contracts
3. CORE ARCHITECTURE
Multi-Round System
Unique design: Game runs multiple rounds simultaneously. Each round has:
- Independent databases (r10_, r11_, r12_, etc.)
- Start/end timestamps
- Type (normal, supporters-only)
- Speed (turns per 10 mins)
- Max build limit
- Turn reserves
- Credit add-on costs
- Max crew size
Round lifecycle:
`php
$game = mysql_fetch_array(mysql_query("SELECT round,ends,starts FROM $tab[game] WHERE ends>$time ORDER BY round ASC;"));
if ($game[2] > $time) {
echo "starts in " . countdown($game[2]);
} else {
echo "ends in " . countdown($game[1]);
}
`
Entry Point (index.php)
`php
include("html.php");
$html = mysql_fetch_array(mysql_query("SELECT description FROM $tab[html];"));
// Display news (last 5 posts)
$getnews = mysql_query("SELECT id,news,posted FROM $tab[news] WHERE id>0 ORDER BY posted DESC limit 5;");
// Show active rounds with top 10 rankings
$getgames = mysql_query("SELECT round,ends,starts FROM $tab[game] WHERE ends>$time ORDER BY round ASC;");
while ($game = mysql_fetch_array($getgames)) {
$getpimps = mysql_query("SELECT pimp,networth,nrank,crew FROM r".$game[0]."_pimp WHERE rank>0 ORDER BY nrank ASC LIMIT 10;");
// Display top 10 pimps with crew icons
}
`
Core Functions (funcs.php)
`php
function fetch($query) {
$data = mysql_fetch_row(mysql_query($query));
return $data[0];
}
function commas($str) {
return number_format(floor($str));
}
function countdown($online) {
// Days, hours, mins, secs display
global $time;
$difference = $online - $time;
// Calculate days/hours/mins/secs
}
function securepic($var) {
// Blacklist banned image URLs (goatse, tubgirl, etc.)
if(strstr($var,"diamondswebpages")) { $var="gfx/media/banned.gif"; }
// Multiple blocked shock sites
}
`
Session Management (html.php)
`php
function secureheader() {
global $id, $tab, $time;
$user = mysql_fetch_array(mysql_query("SELECT online,status,code FROM $tab[user] WHERE id='$id';"));
$idle = $time - $user[0];
if (!$user) {
setcookie("trupimp", NODATA);
header("Location: login.php?reason=notlogged");
}
elseif ($idle > 3600) { // 1 hour idle timeout
setcookie("trupimp", NODATA);
header("Location: login.php?reason=idle");
}
elseif ($user[1] == banned) {
setcookie("trupimp", NODATA);
header("Location: login.php?reason=banned&code=$user[2]");
}
mysql_query("UPDATE $tab[user] SET online='$time' WHERE id='$id';");
}
`
4. GAMEPLAY FEATURES
Pimp Character System
70+ columns in r#_pimp table:
Core Stats:
pimp- Player nameuser- Associated usernamepass,email- Account credentialstrn- Turns availableres- Reserved turnsmoney- Cash on handnetworth- Total value (ranking metric)rank,nrank- Current/new ranking position
Assets:
whore- Number of prostituteswhappy- Hoe happiness (1-100)payout- Payment percentage to hoescondom- Condom supplymedicine- Medical suppliesthug- Number of thugs/bodyguardsthappy- Thug happiness (1-100)weed- Weed supply (for thugs)crack- Crack supplylowrider- Vehicles owned
Weapons:
glock- Glocks ownedshotgun- Shotgunsuzi- Uzisak47- AK-47s
Combat Stats:
attin- Times attacked (incoming)attout- Times attacked others (outgoing)attackout- Total outgoing attack valueattackin- Total incoming attack valuelastattack- Timestamp of last attacklastattackby- Who attacked you lastwhorek- Hoes killedthugk- Thugs killed
Social:
crew- Gang membership IDcity- Home city IDmsg- New message countmsgsent- Total messages sentivt- Crew invitations pendingcmsg- Crew messages unreadprofile- Profile image URLdescription- Profile text
Protection:
protection- Protection time remainingprotectstarted- When protection beganpostpriv- Board posting privilege
System:
online- Last activity timestampip,host- Connection infocode- Unique code (MD5 hash)pin- Security PINstatus- normal/banned/adminsounds- Sound effects enabled/disableddefaultturns- Default turn allocationcanadd- Maximum hoes addable
Crew (Gang) System
crew.php (428 lines):
- Create/join crews (gangs)
- Crew rankings by networth
- Founder/co-founder roles
- Member management
- Crew icon (14x14 pixel image)
- Crew profile page
- City-based crews
- Crew message boards
Crew invitations:
`sql
CREATE TABLE r10_invites (
id mediumint(8) unsigned NOT NULL auto_increment,
crew bigint(20) NOT NULL default '0',
pimp bigint(20) NOT NULL default '0',
cancelled char(3) NOT NULL default 'no',
PRIMARY KEY (id)
) TYPE=MyISAM AUTO_INCREMENT=17;
`
City System
Multiple cities per game:
- Players start in chosen city
- City rankings
- Crew territories
- City-specific boards
Turn-Based Gameplay
Turn regeneration:
- Configurable speed (e.g., "2 turns every 10 mins")
- Reserved turns (accumulates while offline)
- Turn add-ons via credits (PayPal)
Turn consumption:
- Attacking other players
- Managing hoes/thugs
- Purchasing items
- Trading
Combat/Attack System
wanted table:
`sql
CREATE TABLE r10_wanted (
target int(11) NOT NULL default '0',
whore int(11) NOT NULL default '0',
thug int(11) NOT NULL default '0',
msg varchar(255) NOT NULL default '',
attacker varchar(32) NOT NULL default ''
) TYPE=MyISAM;
`
Attack mechanics:
- Hit contracts on players
- Weapon calculations (glock/shotgun/uzi/ak47)
- Hoe vs hoe combat
- Thug vs thug combat
- Kill counts tracked
- Revenge system (lastattackby)
Message System
mailbox table:
`sql
CREATE TABLE r10_mailbox (
id bigint(20) unsigned NOT NULL auto_increment,
src int(11) NOT NULL default '0', -- Sender
dest int(11) NOT NULL default '0', -- Recipient
msg text NOT NULL,
time int(12) NOT NULL default '0',
inbox varchar(32) NOT NULL default '',
del char(3) NOT NULL default 'no',
crew int(11) NOT NULL default '0'
) TYPE=MyISAM AUTO_INCREMENT=935;
`
Board System
Multiple boards:
- Public board
- Crew-specific boards
- Attack boards (trash talk)
- Admin posts (distinguished)
- Message status (new/read)
Awards System
awards.php (374 lines):
- Achievement tracking
- Winner history
- Round winners
- Hall of fame
Payment Integration
PayPal IPN (ipn.php):
`sql
CREATE TABLE paypal (
tranid varchar(32) NOT NULL default '',
amount varchar(32) NOT NULL default '',
fee varchar(32) NOT NULL default '',
user varchar(32) NOT NULL default '',
datebought int(11) NOT NULL default '0'
) TYPE=MyISAM;
`
Credits system:
- Purchase credits via PayPal
- Credits buy extra turns
- Supporters-only rounds
- Premium features
5. SECURITY ANALYSIS
Authentication
Login (login.php):
`php
$user = mysql_fetch_array(mysql_query("SELECT id,status,code,email,ip FROM $tab[user] WHERE username='$username' AND password='$password';"));
if($user[1] == banned) {
header("Location: login.php?reason=banned&code=$user[2]");
}
elseif($user[1] == unverified) {
header("Location: confirm.php?email=$user[3]");
}
elseif($user) {
$host = gethostbyaddr("$REMOTE_ADDR");
mysql_query("UPDATE $tab[user] SET online='$time', ip='$REMOTE_ADDR', lastip='$user[4]', host='$host' WHERE id='$user[0]';");
setcookie("trupimp", $user[2]);
header("Location: myaccount.php");
}
`
CRITICAL FLAW: Direct POST variables in SQL without escaping!
`php
WHERE username='$username' AND password='$password'
`
Password Handling
Registration (signup.php):
`php
$code = md5($username . trucode . $password);
$pin = md5($email . trucode);
mysql_query("INSERT INTO $tab[user] (username,password,email,fullname,age,messager,online,ip,host,code,membersince) VALUES ('$username','$password','$email','$first $last','$age','$messager: $messager_id','$time','$REMOTE_ADDR','$host','$code','$time');");
`
PLAINTEXT PASSWORDS! Stored directly in database without hashing.
Email confirmation (confirm.php):
`php
$checkpin = md5($email . trucode);
`
SQL Injection Vulnerabilities
Widespread lack of escaping:
`php
// NO mysql_real_escape_string() anywhere!
// NO prepared statements
// Direct variable insertion into queries
`
Examples:
`php
$user = mysql_fetch_array(mysql_query("SELECT * FROM $tab[user] WHERE username='$username';"));
$pimp = mysql_fetch_array(mysql_query("SELECT pimp FROM r$round_$tab[pimp] WHERE pimp='$pimp';"));
mysql_query("UPDATE $tab[user] SET Password='$newpass' WHERE id=$id");
`
XSS Prevention
No output encoding observed. Direct echo of user input:
`php
`
Image Blacklist
securepic() function (funcs.php):
`php
function securepic($var) {
if(strstr($var,"diamondswebpages")) { $var="gfx/media/banned.gif"; }
elseif(strstr($var,"http://mywebpages.comcast.net/wahtever/")) { $var="gfx/media/banned.gif"; }
elseif(strstr($var,"http://thunder.prohosting.com/~csears/WeBmAsTeR.swf")) { $var="gfx/media/banned.gif"; }
elseif(strstr($var,"http://www.rentyman.com/temp/rentyman.swf")) { $var="gfx/media/banned.gif"; }
elseif(strstr($var,"http://www.millsracing.com/images/fatguyeating.gif")) { $var="gfx/media/banned.gif"; }
elseif(strstr($var,"http://www.redcoat.net/pics/tubgirl.jpg")) { $var="gfx/media/banned.gif"; }
elseif(strstr($var,"pimpwarhelp.com")) { $var="gfx/media/banned.gif"; }
return $var;
}
`
Purpose: Blocks shock sites (goatse, tubgirl) and competitor sites (pimpwar).
Session Security
Cookie-based authentication:
`php
setcookie("trupimp", $user[2]); // Stores user code
`
- Idle timeout (1 hour)
- IP/hostname tracking
- No session regeneration
- Predictable MD5 code (username + constant + password)
- No CSRF protection
Ban System
IP-based banning:
`php
$host = gethostbyaddr("$REMOTE_ADDR");
$getbans = mysql_query("SELECT banned FROM $tab[banned];");
$bans = array();
while($ban = mysql_fetch_array($getbans)) {
array_push($bans, $ban[0]);
}
foreach ($bans as $correct) {
if(strstr($host, "$correct")) {
$banreason = mysql_fetch_array(mysql_query("SELECT reason FROM $tab[banned] WHERE banned='$correct';"));
// Display ban message
$lamerstop = bitch;
}
}
`
Features:
- Hostname-based blocking
- Ban reasons stored
- Permanent bans
- Account status tracking
Input Validation
Username validation:
`php
if ((!preg_match('/^[a-z0-9][a-z0-9\.\-_]*$/i', $username)) || (strstr($username,"."))) {
$msg = "Invalid username: a-Z 0-9 -_ charactors only.";
}
elseif ((strlen($username) <= 2) || (strlen($username) >= 19)) {
$msg = "Invalid username: must be at least 3-18 in length.";
}
`
Password validation:
`php
if ((!preg_match('/^[a-z0-9][a-z0-9\.\-_]*$/i', $password)) || (strstr($password,"."))) {
$msg = "Invalid password: a-Z 0-9 -_ charactors only.";
}
elseif ((strlen($password) <= 2) || (strlen($password) >= 13)) {
$msg = "Invalid password: must be at least 3-12 in length.";
}
`
Email validation:
`php
if (!ereg("^.+@.+\\..+$", $email)) {
$msg = "Invalid email: that is not a valid e-mail address.";
}
`
Age restriction:
`php
if (($age <= 13) || ($age >= 80)) {
$msg = "Invalid age: you must be 14 years or older to play.";
}
`
SECURITY RATING: 2/10
CRITICAL VULNERABILITIES:
- PLAINTEXT PASSWORDS - Catastrophic security flaw
- NO SQL ESCAPING - Trivial SQL injection everywhere
- NO XSS PROTECTION - Direct output of user data
- PREDICTABLE USER CODES - MD5(username + constant + password)
- NO CSRF PROTECTION - State-changing actions unprotected
- mysql_* FUNCTIONS - Deprecated, no prepared statements
MINOR POSITIVES:
- Idle timeout enforcement
- IP/hostname tracking
- Input format validation (username/password regex)
- Email confirmation system
- Ban system with reasons
VERDICT: One of the worst security implementations in this collection. Comparable to 2003-era scripts before security awareness. TOTALLY UNSAFE for public deployment.
6. TECHNICAL OBSERVATIONS
Multi-Round Database Design
Clever approach: Each game round gets independent table set (r10_, r11_, r12_):
- Allows parallel rounds without data conflicts
- Historical rounds remain intact
- Easy round archival
- Increased database size (duplicate schemas)
Pros:
- Clean data separation
- No round ID in every query
- Simple backup/restore per round
Cons:
- Schema duplication (maintenance nightmare)
- Cannot query across rounds easily
- Database bloat with many rounds
Timestamped Image Files
483 files named like: .gif1096810374, .jpg1098455668
Likely explanation: User-uploaded images stored with Unix timestamp. No file extension normalization:
`
colors.jpg -> Normal static asset
.jpg1098455668 -> Uploaded 2004-10-22 (timestamp 1098455668)
.gif1106679765 -> Uploaded 2005-01-25 (timestamp 1106679765)
`
Security concern: No upload validation, direct timestamp naming allows enumeration of all uploads.
Email System
Dual mail functions:
`php
function mail_1($subject, $message, $email) {
mail("$email", "$subject", $message,
"From:
."Reply-To:
."X-Mailer: PHP/" . phpversion());
}
function mail_2($subject, $message, $email) {
$MP = "/usr/sbin/sendmail -t";
$fd = popen($MP, "w");
fputs($fd, "To: $email\n");
fputs($fd, "From: PimpAttack
fputs($fd, "Subject: $subject\n");
fputs($fd, "X-Mailer: PHP4\n");
fputs($fd, $message);
pclose($fd);
}
`
Redundancy: Both functions called on signup. Backup system if mail() fails?
Google AdSense Integration
`javascript
`
Monetization: Ad-supported game with premium credit purchases.
Turn Cron System
Automated turn regeneration:
`sql
CREATE TABLE r10_cronjobs (
cronjob varchar(32) NOT NULL default '0',
lastran int(12) NOT NULL default '0'
) TYPE=MyISAM;
`
Cron scripts:
- 10mins.php - 10-minute tasks (turn regeneration)
- 5mins.php - 5-minute tasks
- 1hour.php - Hourly tasks
Alternative Version: "tru" Folder
coregames.co.uk branding:
`html
copyright © 2004 Core Games. all rights reserved
`
Possible white-label version for Core Games hosting. Same game, different branding.
Mr_Pfänner Folder
Contains: Version 0.0.1 reference
German developer? "Pfänner" is German word. Possibly early development version or contributor's personal build.
7. HISTORICAL CONTEXT
Browser Game Boom (2003-2005)
PimpAttack represents the "urban crime" subgenre of browser games popular in mid-2000s:
- Pimpwar (original, circa 2002)
- Kings of Chaos (army-building, 2002)
- Mafia MoFo
- Gangster Paradise
- Pimp Game
Theme trend: "Edgy" subject matter (crime, violence, drugs, prostitution) attracted teenage male demographic.
Technology Era Markers
2004-2005 signatures:
- PHP4 (X-Mailer: PHP4)
- mysql_* functions (PHP 5.0-5.6)
- MyISAM tables (no foreign keys)
- No prepared statements
- Short PHP tags (
- register_globals era ($username from POST)
- phpMyAdmin 2.6.1-rc1
PayPal Integration
Early micropayments: PimpAttack pioneered premium credits before:
- Facebook Credits (2009)
- Freemium became mainstream
- App store IAPs
Credits.php (234 lines) - sophisticated payment system for 2004 standards.
Competitive Landscape
Meta keywords:
`html
'pimp, pimp game, pimping game, multiplayer game, free game, ho, hoe, hoes, gangster, mafia, multiplayer, strategy, player, gang war, crack, drugs, free game, beat down, smack down, pimping, prostitution game, mmog, massively multiplayer online game, turn based game, flash game'
`
SEO targeting: "similar to pimpwar and kings of chaos" - riding competitors' search traffic.
Cultural Context
2004 "shock gaming":
- Pre-social media era
- Edgier content acceptable online
- "Gangsta" culture influence (rap music, GTA games)
- Less corporate oversight
- Anonymous development common
Modern perspective: Subject matter now considered inappropriate for most platforms. Would struggle with app store guidelines, payment processor ToS, and advertising partners.
8. COMPLETENESS & PLAYABILITY
Implemented Features
Core gameplay:
- Multi-round system
- Turn-based mechanics
- Character management (hoes/thugs/weapons)
- Combat/attack system
- Crew (gang) system
- City-based gameplay
- Rankings (individual + crew)
- Private messaging
- Message boards
- Profile system
- Email confirmation
- PayPal integration
- Credits system
- Awards/achievements
- Admin panel
- Ban system
- News system
- Idle timeout
- Protection system
- Contacts (friends/enemies)
- Wanted (hit) system
Missing/Incomplete
- No mobile interface
- No API
- Limited documentation
- No game guide (empty?)
- Sound effects mentioned but not implemented
- Some image paths broken (gfx/media/)
Playability: 85%
Core loop functional:
- Register account
- Join game round
- Choose city
- Name pimp character
- Manage resources (hoes, thugs, weapons)
- Attack other players
- Join crew
- Climb rankings
- Use credits for advantages
- Start over in new rounds
Database completeness: Empty SQL file provided for fresh installations. Cronjob tables suggest automated systems work.
9. COMPARISON TO COLLECTION
Unique Features
- Multi-round system - Only game with parallel rounds
- PayPal integration - First with real-money transactions
- Timestamped image uploads - 483 user-uploaded files
- Crew icons - 14x14px gang symbols
- Per-round databases - Independent r#_ table sets
- Protection system - Temporary immunity from attacks
- Wanted contracts - Player bounties
- Turn reserving - Save turns while offline
Genre Comparison
vs other crime games:
- More complex than basic mafia RPGs
- Multi-round structure unique
- PayPal credits more sophisticated than most
- Crew system more developed than typical gang features
vs character RPGs:
- Resource management (hoes/thugs) instead of HP/MP
- Turn-based instead of time-based
- Competitive rankings primary goal
- No quest system
- No NPC interactions
Security Comparison
Worst security in collection:
- Plaintext passwords (unprecedented)
- No SQL escaping (matched only by earliest games)
- No XSS protection (common in 2004, unacceptable now)
Even early RPGs (2003-2004) had:
- MD5 password hashing
- Some SQL escaping
- Better validation
Codebase Size
6,954 lines - Mid-range:
- Smaller than: MCCodes (67K), Orodin (107K), phpRPG (13K)
- Larger than: phpSGE (5.8K)
- Similar to: Many standalone games (5-10K lines)
10. RATING & VERDICT
Overall Rating: 4/10
Breakdown:
- Code Quality: 3/10 (functional but insecure)
- Security: 2/10 (plaintext passwords, no SQL escaping)
- Features: 8/10 (comprehensive gameplay, PayPal, multi-round)
- Innovation: 7/10 (unique round system, early monetization)
- Playability: 8/10 (85% complete, core loop works)
- Documentation: 2/10 (minimal, no guide)
Tier Classification: LOW-TIER (Security Concerns)
Strengths
- Innovative multi-round system - Play multiple games simultaneously
- Early monetization - PayPal integration in 2004 (pioneering)
- Complete gameplay loop - All core features functional
- Crew system - Sophisticated gang mechanics
- Turn reservation - Offline turn accumulation
- Protection system - Newbie protection implemented
- Per-round databases - Clean data separation
- Awards system - Achievement tracking
- Ban system - IP/hostname blocking with reasons
- Idle timeout - Automatic logout security
Critical Weaknesses
- PLAINTEXT PASSWORDS - Unforgivable security flaw
- NO SQL ESCAPING - Trivial SQL injection everywhere
- NO XSS PROTECTION - Direct user input output
- DEPRECATED mysql_* - Old PHP functions
- Controversial theme - Prostitution/drugs/violence (2004-acceptable, now problematic)
- Database bloat - Per-round schema duplication
- No documentation - Empty guide
- Minimal validation - Format checks only
- Short PHP tags - (
- No CSRF protection - State changes unprotected
Historical Significance
Important for:
- Early browser game monetization - PayPal integration in 2004
- Multi-round architecture - Innovative parallel game design
- Urban crime genre - Represents "edgy gaming" era (2003-2006)
- Technical archaeology - Pure 2004 PHP4 codebase snapshot
Cultural artifact: Captures mid-2000s internet culture:
- Anonymous development
- Shock value themes
- Ad-supported with premium upsells
- No corporate oversight
- Pre-social media gaming
Modern Deployment
NOT RECOMMENDED for production:
- Plaintext passwords = instant compromise
- SQL injection = database takeover
- Payment processor ToS violations (security requirements)
- Theme inappropriate for modern platforms
- mysql_* deprecated (PHP 7+ incompatible)
Historical/educational use only.
Recommendation
For 2004 standards: 6/10 (innovative features, poor security typical of era)
For 2025 deployment: 1/10 (catastrophic security, deprecated code)
Best aspects: Multi-round system, early monetization, complete gameplay loop
Worst aspects: Plaintext passwords, no SQL escaping, controversial theme
Comparison: More feature-rich than basic mafia games, but security worse than any game analyzed. PayPal integration and multi-round system show ambition, but implementation quality sacrificed for features.
Would need complete security rewrite:
- bcrypt password hashing
- Prepared statements (PDO/mysqli)
- XSS output encoding
- CSRF tokens
- Session regeneration
- Input sanitization
- Modern PHP 8.x
- Content policy review
Historical value: Excellent example of 2004-era browser gaming boom. Shows evolution of micropayment systems and innovative round-based architecture that became standard in modern idle/incremental games.
---
Analysis Date: December 11, 2025
Archive Location: d:\_HOUSE\SOCIALMUD\WWW\_MUD Games\unzipped\pimp_attack\PimpAttack\
Game #55 of 79 in systematic browser game analysis project
Security Warning
Running many of the scripts in this archive on a live server presents a serious security risk. These projects were created before modern hardening practices and may contain vulnerabilities that can compromise your system.
We strongly recommend using this code for reference and analysis only, or in isolated local environments. By downloading these files, you accept full responsibility for their use.